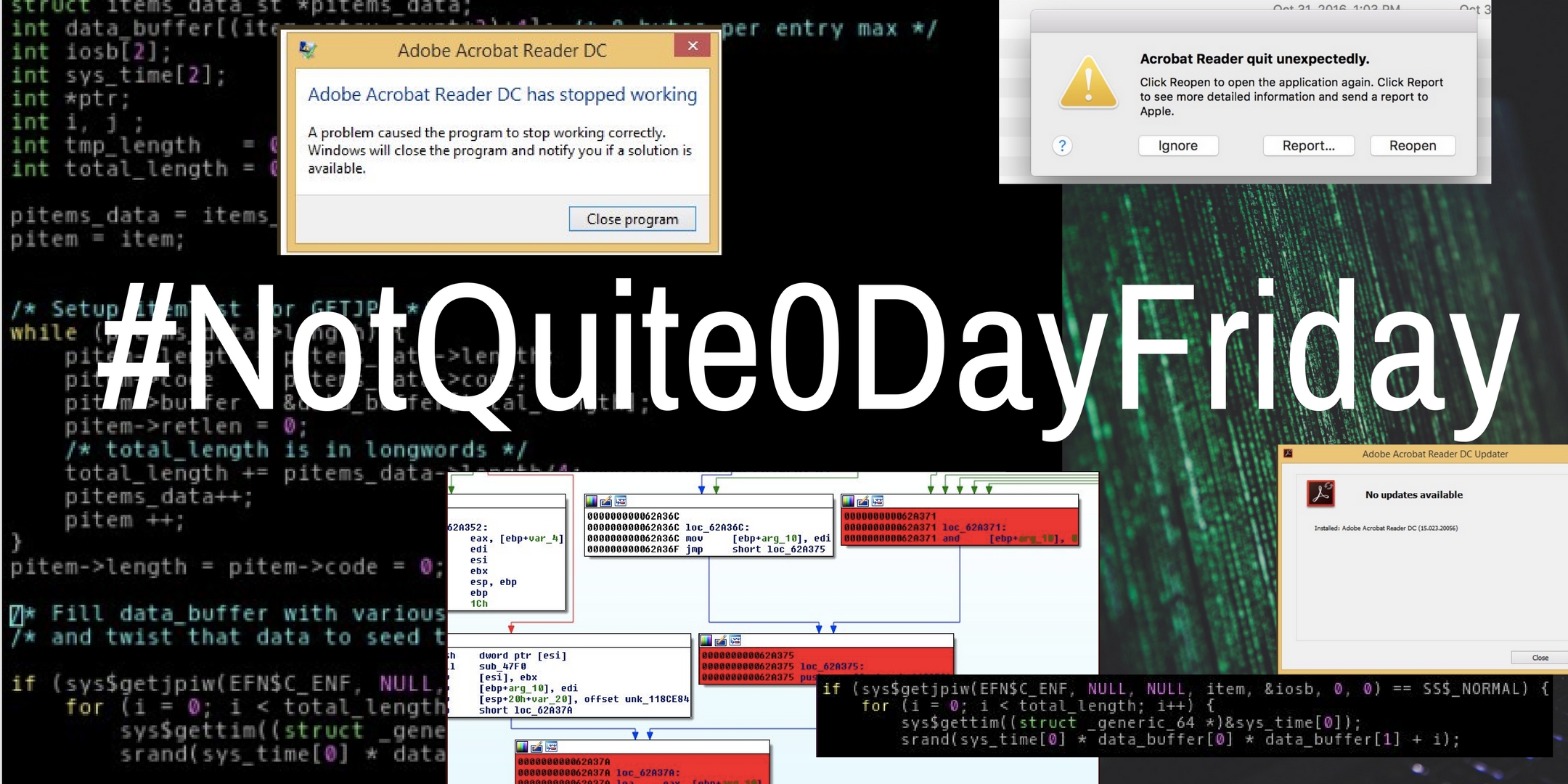
#NotQuite0DayFriday
In our spare time, we like to hunt for bugs in various pieces of software. To help teach people this skill, we decided to write up our analysis on some of the crashes we find. The goal is to help people learn how to debug, analyze the problem, determine why it’s happening, and what the impact is. For example, is this just something which will cause the software to crash and merely cause a brief denial of service, or is this a vulnerability which can be exploited to take complete control over the computer?
We follow NIST’s example and privately disclose the details of the issue to the software producers and then to the public either when the vendor tells us the issue is patched, isn’t going to be patched, or 45 days elapses. This is intended to protect the software users.
We call it Not Quite 0-Day Friday because most of the bugs are 0-day vulnerabilities when we find them, but recently patched when we release them. So they’re not quite 0-days at the time of release. Most of the time the issues are patched quickly and a new release is pushed out to users within a matter of days, but there have been some cases where the vendor didn’t patch the issue within the 45-day deadline in which case they were still 0-days at the time of public disclosure, but these are the exception, not the rule.
Why do we do this? Finding bugs, coordinating disclosure, writing up and publishing details on the issue and the impact doesn’t pay the bills, but there are several reasons we do this anyway. First and foremost, we think it’s fun to find the bugs that everyone else has overlooked and figure out what can be done with them. We also like teaching others how to do this type of work so they can join us in finding bugs. It also serves as a public demonstration of our technical skills. There are a lot of people and companies out there who make a lot of tall claims and it can be difficult to tell who is all hype and who is the real deal. We hope that other companies out there who can walk the walk will join us in publishing some of their work. Finally, it arguably makes software more secure in a number ways. The bugs we find are generally getting patched as a result of this work. If others join in and help scale up this effort, it helps the software vendors who do invest in security stand out amongst their competitors and gives users the ability to make an educated decision, rather than a decision based on marketing and propaganda. Ultimately, we think that #NotQuite0DayFriday is an effective tool for educating the general public, teaching our colleagues, and hopefully, making the Internet a safer place for all of us.